VP Mentor report
In this case,we easily identified THSuite as the owner of the database and contacted the company with our findings.
- Date discovered: December 24, 2019
- Date owners contacted: December 26, 2019
- Date Amazon AWS contacted: January 7, 2020
- Date database closed: January 14, 2020
Click on image to access THSuite website
These are some of their partners who might not be that enthused by the news
Here’s the introduction to a very detailed report by VPNMentor
Report: Cannabis Users’ Sensitive Data Exposed in Data Breach
Led by internet privacy researchers Noam Rotem and Ran Locar, vpnMentor’s research team discovered adata breach in THSuite, a point-of-sale system in the cannabis industry.
Our team identified an unsecured Amazon S3 bucket owned by THSuite thatexposed sensitive data from multiple marijuana dispensariesaround the US and their customers.
The leaked data includedscanned government and employee IDs, exposing personally identifiable information (PII) for over 30,000 individuals.
THSuite Company Profile
THSuite offers business process management software services to cannabis dispensary owners and operators in the US.
Cannabis dispensaries have to collectlarge quantities of sensitive information in order to comply with state laws. The THSuite platform is designed to simplify this process for dispensary operators by automatically integrating with each state’s API traceability system.
As a consequence of this, the platform has access to a lot of private data related to dispensaries and their customers.
Timeline of Discovery and Owner Reaction
Sometimes the extent of a data breach and the owner of the data are obvious, and the issue quickly resolved. But rare are these times. Most often,we need days of investigation before we understand what’s at stake or who’s leaking the data.
Understanding a breach and its potential impact takescareful attention and time.We work hard to publishaccurate and trustworthy reports, ensuring everybody who reads them understands their seriousness.
Some affected parties deny the facts, disregarding our research or playing down its impact. So, we need to be thorough and make sure everything we find is correct and true.
In this case,we easily identified THSuite as the owner of the database and contacted the company with our findings.
- Date discovered: December 24, 2019
- Date owners contacted: December 26, 2019
- Date Amazon AWS contacted: January 7, 2020
- Date database closed: January 14, 2020
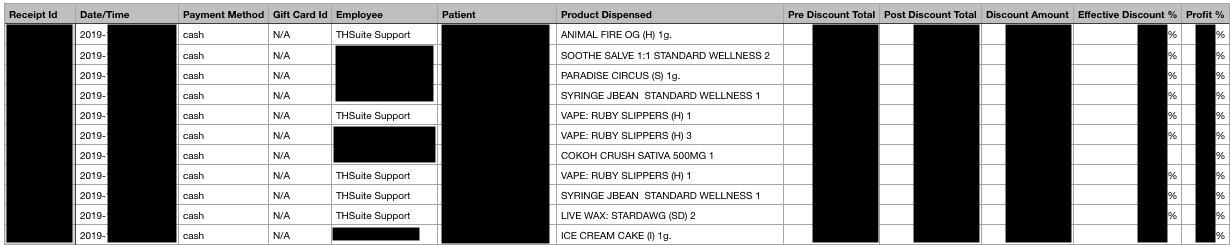
Example of Entries in the Database
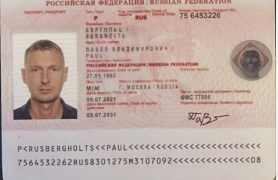
Over 85,000 fileswere leaked in this data breach, includingover 30,000 records with sensitive PII. The leak also included scanned government and company IDs stored in an Amazon S3 bucket through the Amazon Simple Storage Service.
The leaked bucket contained so much data thatit wasn’t possible for us to examine all the records individually. Instead, we looked through a handful of random entries to understand what types of data were exposed in the breach overall.
In the sample of entries we checked, we found information related to three marijuana dispensaries in different locations around the US: Amedicanna Dispensary, Bloom Medicinals, and Colorado Grow Company. Examples of these entries can be found below.
However, this breach affected many more dispensaries.It’s possible that all THSuite clients and their customers were involved.
We also found photographs ofgovernment-issued photo IDsand corresponding signatures of dispensary visitors and patients alike. Additionally, there are attestations for what appears to be each patient acknowledging state laws regarding purchase and use of cannabis-based medicine.
Amedicanna Dispensary Files
The THSuite breach involved data from AmediCanna Dispensary, a medical marijuana dispensary located in the state of Maryland.
The leak exposed the following personal details about Amedicanna’s customers:
- Full name
- Phone number
- Email address
- Date of birth
- Street address
- Medical/State ID number and expiration date
- Cannabis gram limit
- Signature
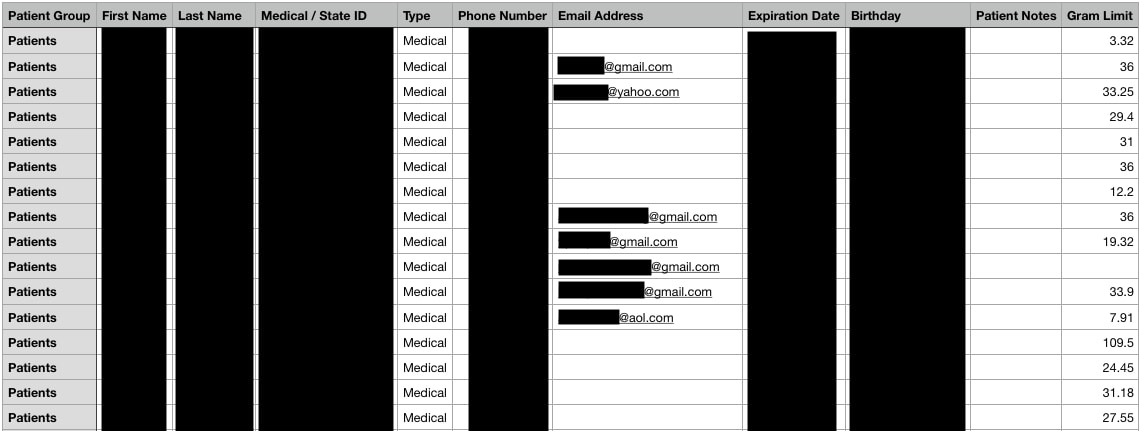
The database also includeddetails about Amedicanna’s inventory and sales. We were able to view a list of transactions with the following information:
- Patient name and medical ID number
- Employee name
- Cannabis variety purchased
- Quantity of cannabis purchased
- Total transaction cost
- Date received, along with an internal receipt ID
Bloom Medicinals
Bloom Medicinals is an Ohio-based medical marijuana dispensary with locations in Akron, Columbus, Maumee, Painesville, and Seven Mile.
The data breach exposed information about the dispensary’sinventory, monthly sales reports, and compliance reports, as well asthe following patient details:
- Full name
- Date of birth
- Medical/State ID and expiration date
- Phone number
- Email address
- Street address
- Date of first purchase
- Whether or not the patient received financial assistance for cannabis purchases
- Whether or not the patient opted in for SMS text notifications
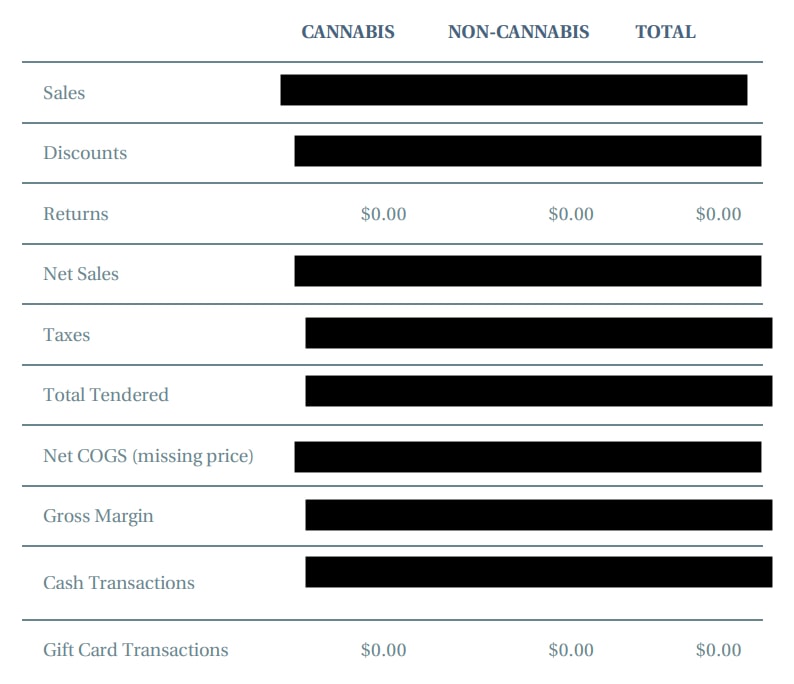
We were able to view the dispensary’s monthly sales, discounts, returns, and taxes paid. The sales were further broken down by payment method and product type.
The database included a list of each cannabis product, along with a brief description, the product’s supplier, and its price.
Colorado Grow Company
Colorado Grow Company is a recreational marijuana dispensary located in the city of Durango, Colorado.
The THSuite data breach exposed the dispensary’s monthly sales reports for both cannabis and non-cannabis products, including gross sales, discounts, taxes, net sales, and totals for each payment type.
The leak exposedfull names of dispensary employees and the number of hours they workedduring each two-week pay period.
Read More at